-
It has been discovered that malicious HTML using special nesting techniques can bypass the depth checking added to DOMPurify in recent releases. It was also possible to use Prototype Pollution to weak…
-
The xz-utils attack involved an ELF library that parsed and modified the global offset table of the OpenSSH server during the runtime linking phase of startup.
I have developed a tool that examines…
-
The vast majority of these are for APIs that have been around forever and no modern project would need to polyfill. A couple of these may be for newer APIs, but even then it's much better to let your …
-
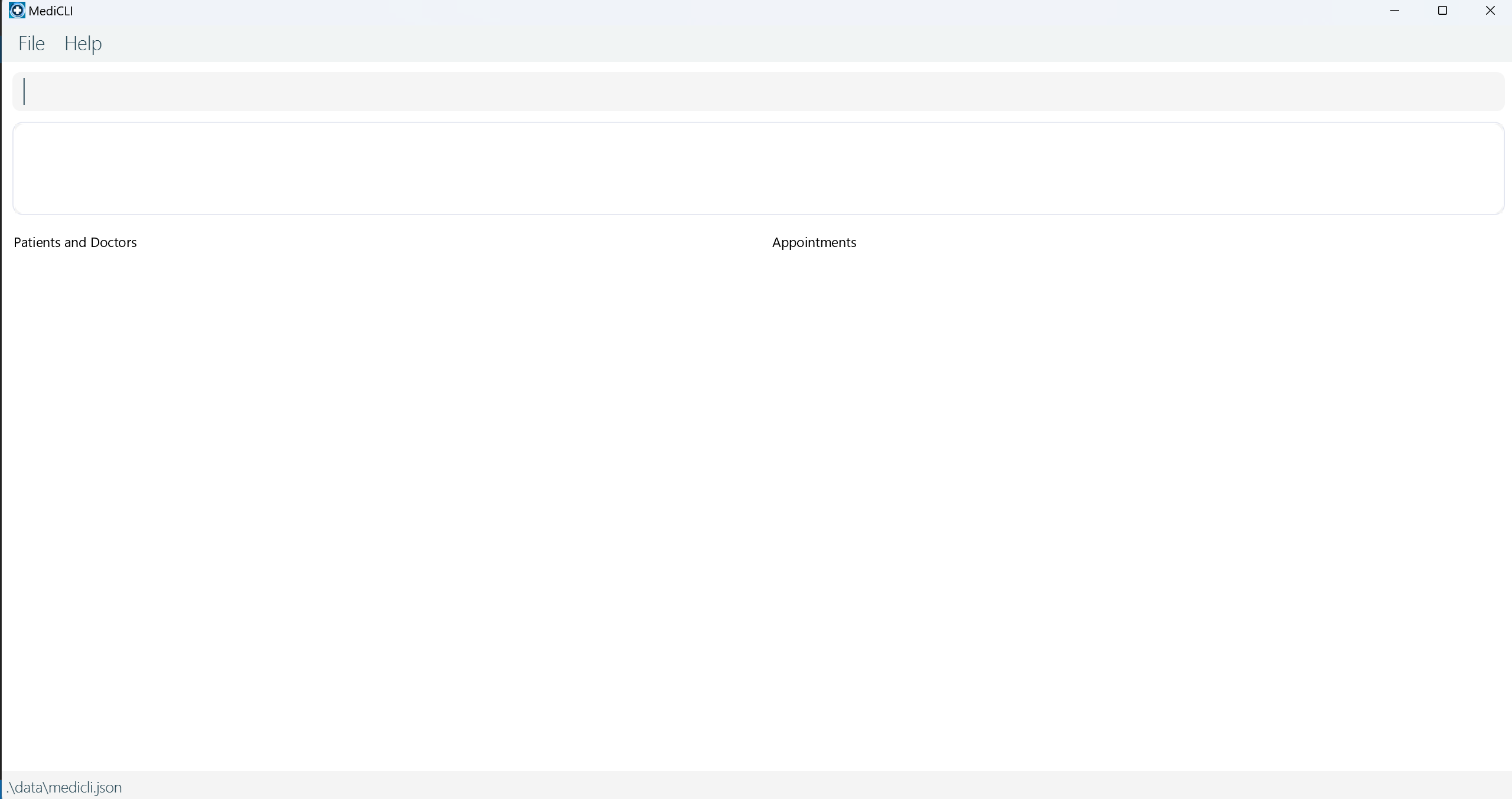
Upon tampering with JSON the entire file disappears. Parts of it should be salvaged.
…
-

Upon tampering with JSON the entire file disappears. Parts of it should be …
-
So I just managed to dynamically modify a single byte in RSA public key through gdb. It is stored little-endian in memory, unlike the original key in `libil2cpp.so`. It should be possible to write a u…
-
**Tier 1: Basic Image Analysis**
Error Level Analysis (ELA):
Function: Analyzes the compression levels of an image to detect inconsistencies.
Importance: A quick, initial method for detecting signs o…
-
I'm trying to wrap my head around the concept, I have the understanding about bitcoin blockchain technology (or others that followed) but I don't seem to understand how scuttlebut can ensure consisten…
-
It's really interesting to see how you've implemented cookies, our team didn't get around to implementing cookies. If you continue working on this project, on top of what you've done already I think y…
-
I saw you mention an option called --verb-tamper in order to bypass jboss 4.X auth
but in the help itself there is no mentioning how to use this option.
can you please give more details regarding on h…