-
! ANY INCOMPLETE REPORT WILL BE CLOSED RIGHT AWAY !
## Steps to Reproduce (for bugs)
1.Open RSF
2. Write scanners
3. Press TAB
4. Get scanners/autopwn scanners/cameras/ scanners/misc/ s…
-
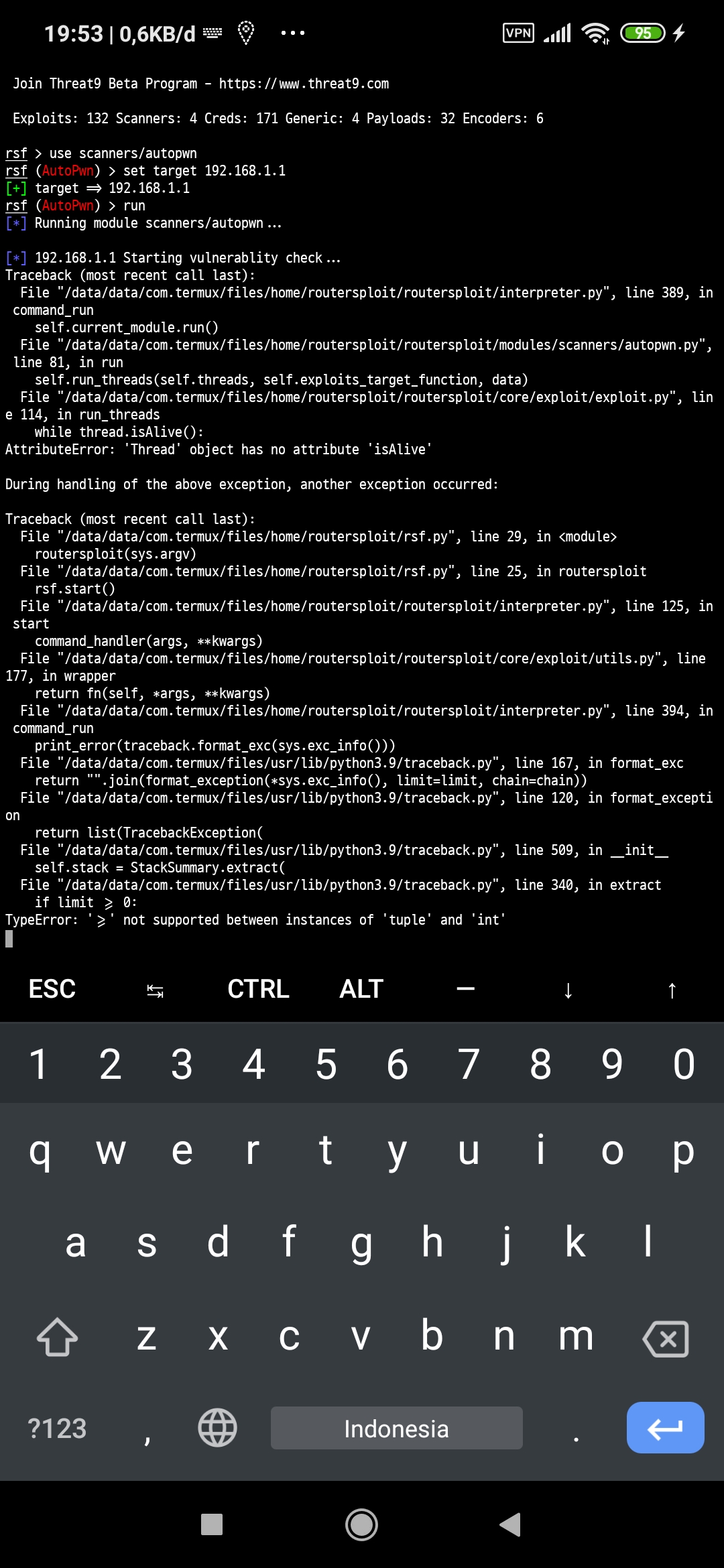
Traceback (most recent call last):
File "/home/ounce/routersploit/routersploit/interpreter.py", line 389, in command_run
self.current_module.run()
File "/home/ounce/routersploit/routersploi…
ghost updated
3 years ago
-
Hi,
I have noticed that since 2016 there were not git releases anymore. Would it be possible to start semi frequent releases again? This would aid packaging routersploit for distro packages.
No sp…
-
rsf > use scanners/routers/router_scan
rsf (Router Scanner) > set target 192.168.1.1
[+] target => 192.168.1.1
rsf (Router Scanner) > run
[*] Running module scanners/routers/router_scan...
[*] …
-
I ignored official form because this is not a bug.
So, what I want:
1. I know you already has armle, mipsle and etc. for elf generator. Is it possible to add aarch64 for it?
2. I saw that Rou…
-
## Steps to Reproduce (for bugs)
1. clone repo
2. run `make test`
## Your Environment
* RouterSploit Version used: 3.4.0, but also reproducible on git master
* Operating System and version: Arc…
-
! ANY INCOMPLETE REPORT WILL BE CLOSED RIGHT AWAY !
## Steps to Reproduce (for bugs)
1. use exploits/routers/multi/tcp_32764_info_disclosure
2. set target IP
3. check
4. run
## Your Environm…
ghost updated
3 years ago
-
-

the self.banner is in __init__ method ,and it's value is a three quotes str…
-
rsf (TCP-32764 RCE) > run
[*] Running module...
[+] Target is vulnerable
[*] Invoking command loop...
[+] Welcome to cmd. Commands are sent to the target via the execute method.
[*] For further…