/dev/rpmb0 exists while /dev/mmcblk0rpmb does not.
But removing either or both doesn't change a bit in the logs.
I also tried to copy the --prot folders /mnt/vendor/persist/t6 and /mnt/vendor/protect_f/tee using -p to even mimicking the timestamps but it didn't help either.
https://github.com/ADeadTrousers/twrp_device_Unihertz_Atom_LXL/commit/0992a63ea338c6356b8f8e4512981df018963b88#diff-e826647ea3da046036fd2fca5b6933d10545a79a77d8361c529881e210b8e845
(This step is required or otherwise the recovery WILL overwrite the files in those folders and the system won't be able to decrypt anymore)
Changing the group of every part that is evolved did do shit also
https://github.com/ADeadTrousers/twrp_device_Unihertz_Atom_LXL/commit/0992a63ea338c6356b8f8e4512981df018963b88
First boot messages look promising
But as soon as it starts to load the certs shit hits the fan
The trustkernel intialization is taken from stock rom https://github.com/ADeadTrousers/twrp_device_Unihertz_Atom_LXL/blob/twrp-11.0-nocrypt/recovery/root/vendor/etc/init/trustkernel.rc#L57
In comparison to the old stock rom a few more parameters need to be set https://github.com/ADeadTrousers/twrp_device_Unihertz_Atom_LXL/blob/twrp-10.0/recovery/root/vendor/etc/init/trustkernel.rc#L54
The most notable one is
--rpmbdevwhich is mentioned in the error messages. But it doesn't help to leave them out. So my guess is thatteedNEEDS those. The same goes with the second--prot.So the whole problem is:
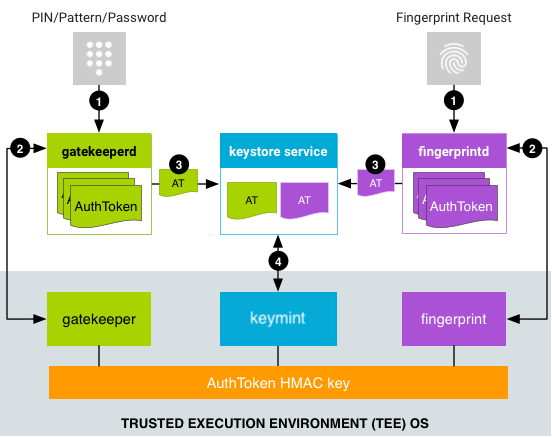
teedis not able to load the certsandroid.hardware.gatekeeper@1.0-serviceis not able to authenticate itself againstteedandroid.hardware.keymaster@4.0-service.trustkernelis not able to authenticate itself againstteedvoldis not able to utilize gatekeeper and keymaster to decrypt TWRP isn't booting, the screen goes blank and after a few seconds the phone reboots.Deactivating
TW_INCLUDE_CRYPTOlets TWRP boot but without decryption.