Just to add to what m'colleague @jmccor99 has said. When we're running SqlAzureDacpacDeployment@1 we can see it's using Invoke-Sqlcmd under the bonnet like so:
Temporary inline SQL file: C:\Users\VssAdministrator\AppData\Local\Temp\tmp604C.tmp
Invoke-Sqlcmd -connectionString "**********" -Inputfile "C:\Users\VssAdministrator\AppData\Local\Temp\tmp604C.tmp"
Sql file: D:\a\1\DbMigrationScript\DbMigrationScript.sql
Invoke-Sqlcmd -connectionString "**********" -Inputfile "D:\a\1\DbMigrationScript\DbMigrationScript.sql" Interestingly, it doesn't pass through -AccessToken as you might expect / hope. This seems surprising.
We did wonder about directly using Invoke-Sqlcmd itself, since it's being used internally, but didn't know whether SqlAzureDacpacDeployment@1 was bringing anything extra to the party that might be useful.
No worries if you don't know / don't have time; but it you've any pointers to share we'd sure appreciate them! ❤️ 🌻

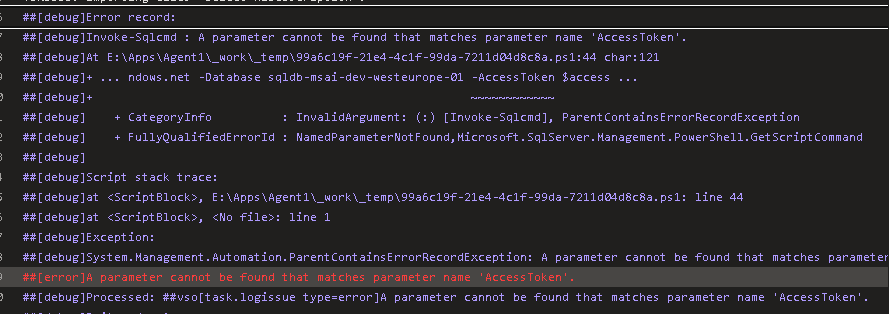
 and other AzurePowerShell@5 task to execute invoke-sqlcmd with accesstoken
and other AzurePowerShell@5 task to execute invoke-sqlcmd with accesstoken

Hello. We are using your example of SqlAzureDacpacDeployment task with access token. We are using SqlTask rather than dacpacFile. We receive [error]Login failed for the user when running the pipeline. The Azure DevOps Service Connection service principal is a member of the SQL Server AADAdmin group. We can use the access token with success outside of the SqlAzureDacpacDeployment task.
This works
This does not work
We would appreciate any insights you could share :)
many thanks,