Subject: RE: Docker for ASP.NET Core 2.1 Preview 2
. Provided that your docker file and docker compose look like the ones that VS generates when you add VS support, there are a couple of steps you need to take to enable it manually. In essence, you need to get the HTTPS development certificate from your machine into the container image as a pfx file in a special location on disk that we recognize and provide the password through user.
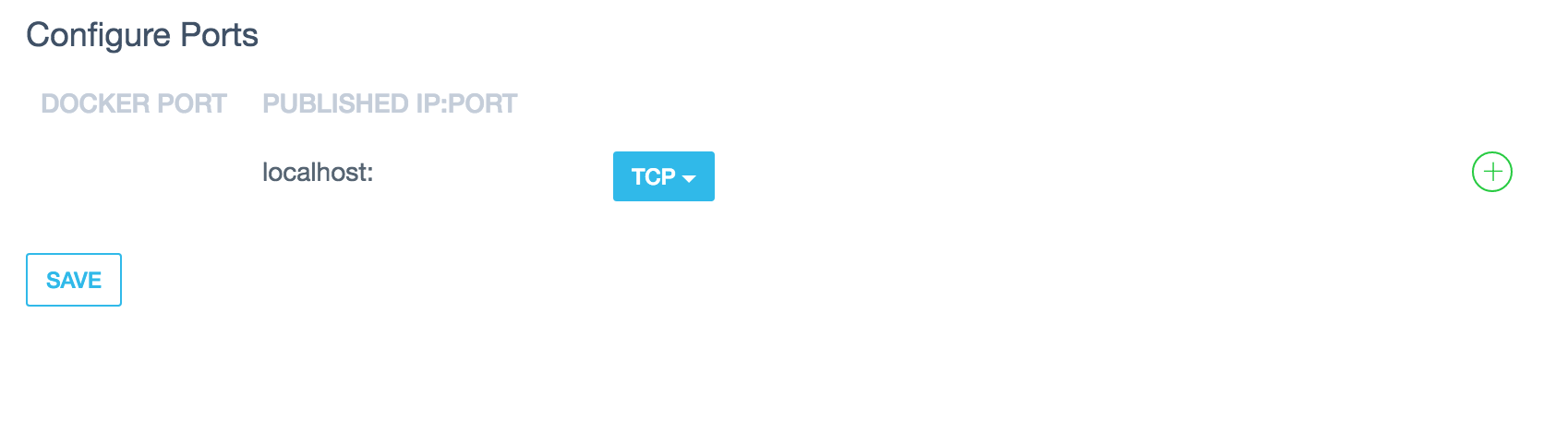
• Modify the dockerfile to expose the port 443 with • EXPOSE 443 • Modify the docker-compose override file to map ports, volumes and environment variables as follows: environment:
- ASPNETCORE_ENVIRONMENT=Development
- ASPNETCORE_URLS=https://+;http://+
- ASPNETCORE_HTTPS_PORT=44349
ports:
Replace the values on the left by the values on your launchSettings.json
- "51217:80"
- "44349:443" volumes:
- ${HOME}/.microsoft/usersecrets/:/root/.microsoft/usersecrets
- ${HOME}/.aspnet/https:/root/.aspnet/https/
• Export the HTTPS certificate into a PFX file using the dev-certs global tool to ${HOME}/.aspnet/https/<
>.pfx using a password of your choice (dotnet dev-certs https -ep ${HOME}/.aspnet/https/ -p < >) • Add the password to the user secrets in your project. • Add the password to the user secrets in your project (dotnet user-secrets set "Kestrel:Certificates:Development:Password" "< >"
per Javier: For setting up a non development certificate on kestrel the instructions are the same as for the development case (obviously you need to provide the certificate) and you need to set the path to the certificate in a configuration key. "Kestrel:Certificates:Default:Path"



 this is after generating user secrets with correct password which was added to appettings.Development.json
also added to docker-compose.override.yml
this is after generating user secrets with correct password which was added to appettings.Development.json
also added to docker-compose.override.yml

related #3310 Javier is contact: This needs to go in Enforce HTTPS in an ASP.NET Core The first time you run dotnet after installing the SDK you get this message Successfully installed the ASP.NET Core HTTPS Development Certificate. To trust the certificate run 'dotnet dev-certs https --trust' (Windows and macOS only). For establishing trust on other platforms please refer to the platform specific documentation. For more information on configuring HTTPS see https://go.microsoft.com/fwlink/?linkid=848054.
Copied from #3310 We also need to cover how to setup the dev certificate when using Docker in development:
Create an application on Visual Studio using the MVC template.
Run the app to ensure its working.
Add docker support for the application through the tooling.
Modify the dockerfile to expose the port 443 with EXPOSE 443
Modify the docker-compose override file to map ports, volumes and environement variables as follows (this will all be unnecessary after docker tooling has support for HTTPS):
Export the HTTPS certificate into a PFX file using the dev-certs global tool to %APPDATA%/ASP.NET/Https/<>.pfx using a password of your choice (recommended password new-guid on powershell)
On your project, open user secrets and add the following configuration keys:
Run your application within the container.
Navigate to the HTTP endpoint on your application