Thank you for this report @nulldowntime and welcome to the Go project!
So the issue here is that for ecdsa.PrivateKey we don't have custom JSON marshaler and unmarhsler methods yet the embedded field Curve is an interface as per:
https://golang.org/pkg/crypto/ecdsa/#PrivateKey

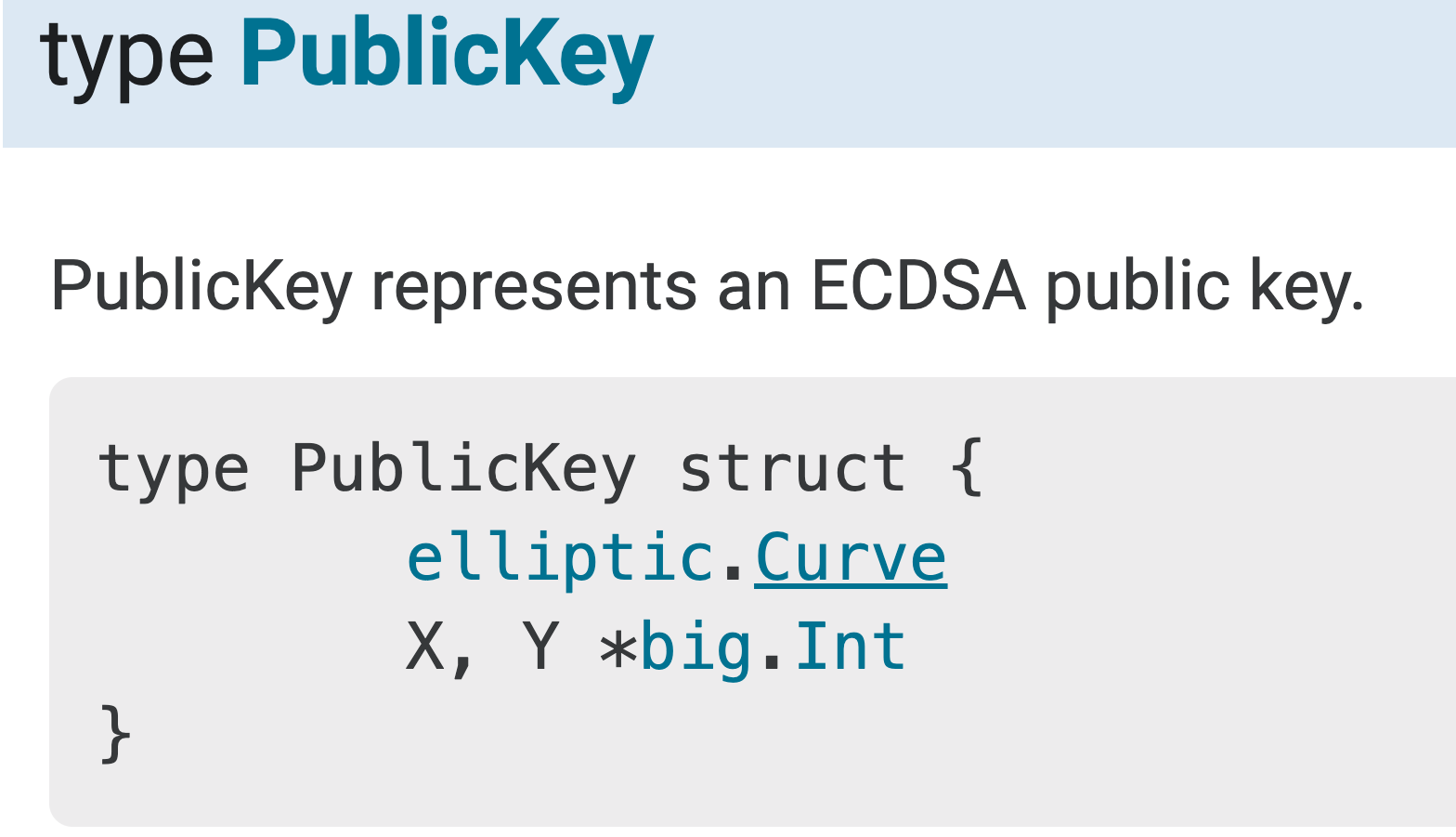
which is an embedded field https://golang.org/pkg/crypto/ecdsa/#PublicKey
and finally https://golang.org/pkg/crypto/elliptic/#Curve

of which a non-nil interface is backed by a concrete type so the JSON.marshal works alright, but not the other way unless we define some custom json.Unmarshaler https://golang.org/pkg/encoding/json/#Unmarshaler methods
You can unmarshal though to the CurveParams as per https://play.golang.org/p/NfTlvFC28Zw or inlined below
package main
import (
"crypto/ecdsa"
"crypto/elliptic"
"crypto/rand"
"encoding/json"
"fmt"
"log"
)
func main() {
privKey, err := ecdsa.GenerateKey(elliptic.P256(), rand.Reader)
if err != nil {
log.Fatalf("Failed to generate privateKey: %v", err)
}
jsonKey, err := json.Marshal(privKey)
if err != nil {
log.Fatalf("error marshalling private key: %v", err)
}
type retrieve struct {
CurveParams *elliptic.CurveParams `json:"Curve"`
}
rt := new(retrieve)
if err := json.Unmarshal(jsonKey, rt); err != nil {
log.Fatalf("error parsing json: %s", err)
}
fmt.Printf("Retrieved.CurveParams: %#v\n", rt.CurveParams)
}which prints out successfully
Retrieved.CurveParams: &elliptic.CurveParams{
P:115792089210356248762697446949407573530086143415290314195533631308867097853951,
N:115792089210356248762697446949407573529996955224135760342422259061068512044369,
B:41058363725152142129326129780047268409114441015993725554835256314039467401291,
Gx:48439561293906451759052585252797914202762949526041747995844080717082404635286,
Gy:36134250956749795798585127919587881956611106672985015071877198253568414405109,
BitSize:256,
Name:"P-256"
}and then for a sample of json.Unmarshaler https://play.golang.org/p/_JvAmJOBe5A
I don't think these structs are normally JSON serialized and unserialized as it has been almost a decade without json interfaces being implemented but I shall defer to the crypto experts @FiloSottile @agl and I shall retitle this issue as a feature request for json.Unmarshaler methods
What version of Go are you using (
go version)?and whatever play.golang.org uses.
Does this issue reproduce with the latest release?
It is the latest release as of now. It can also be reproduced here: https://play.golang.org/p/cbsOhB8lHxe
What operating system and processor architecture are you using (
go env)?go envOutputWhat did you do?
https://play.golang.org/p/cbsOhB8lHxe
What did you expect to see?
A key struct created from json that has just been created from the very same data structure.
The same process does succeed for RSA: https://play.golang.org/p/FFYREV4NMfv , although not on the playground, where I get "Program exited: process took too long." I did test it locally and I'm actually using it as a workaround.
What did you see instead?
error parsing json: json: cannot unmarshal object into Go struct field PrivateKey.Curve of type elliptic.Curve
I have also written the jsonKey to file and verified that it is valid json.