@hashtaginfosec Thanks for another thorough report. Please seem my response in your last issue re pr submissions (#1940) as you are most welcome to submit a pr to address this issue.
Thanks again for your efforts in this area, much appreciated.
@schakrava and @MFlyer more in your areas this one again I'm afraid.
The sessionid cookie does not utilize "secure" flag. Hence, even with the use of TLS, the cookie can be intercepted by listening for pages that may not use TLS. Note that offering the whole website over HTTPS is not a sufficient defense. If a user were to accidentally access the site over HTTP, the server would redirect them to HTTPS; however, that HTTP request has already offered up the cookie "sessionid" to an eavesdropper.
Proof:
Accessing HTTPS site over HTTP: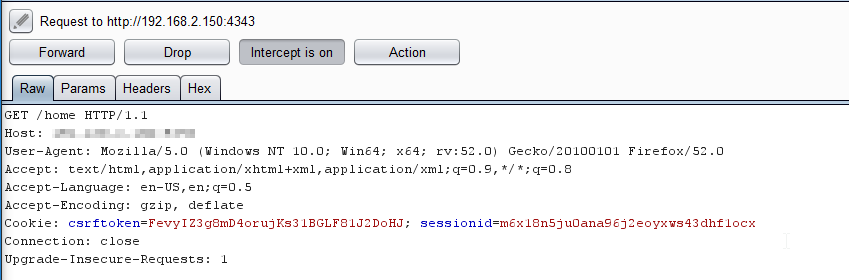
Remediation:
Set-Cookie: <cookie-name>=<cookie-value>; SecureFor more https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Set-Cookie
Possible pitfall: According to Mozilla document referenced above,