~Chromium specific, not reproducible on Firefox.~
Open ghost opened 5 years ago
~Chromium specific, not reproducible on Firefox.~
I could not reproduce with Chromium 70/Linux on my side.
This reminds me of this issue: https://github.com/uBlockOrigin/uMatrix-issues/issues/74 -- though not confirmed by OP, it appears the Cookie header was not being removed by the browser as instructed by uMatrix.
I can reproduce on Chromium 70.0.3538.67/Windows on my end.
@gorhill so a browser bug ? Weird, only happens on that site and nowhere else. Should I close this ?
Btw I'm not affected by #74, if I block cookies, I get logged out, so don't think this is related to that issue.
Ok I could reproduce, I had to allow some 3rd-party scripts in the matrix.
After investigating, I confirm uMatrix really removes the Referer header from request headers.
However, the browser still sets the document.referrer to the original, unmodified header. I consider this to be a browser issue -- I can't even properly provide a workaround for this, only the browser can properly set the correct document.referrer value to match the request header one.
I had to allow some 3rd-party scripts in the matrix.
my bad, forgot to add you need to whitelist ajax.googleapis.com
the browser still sets the document.referrer to the original, unmodified header.
but this website only ? Other referrer testing websites work fine. Is the website triggering some exploit ?
Speaking of document.referrer, it stores the correct value no matter what on any website, below screenshot was taken on https://www.whatsmyreferer.com/ - referrer is spoofed succesfully yet this -
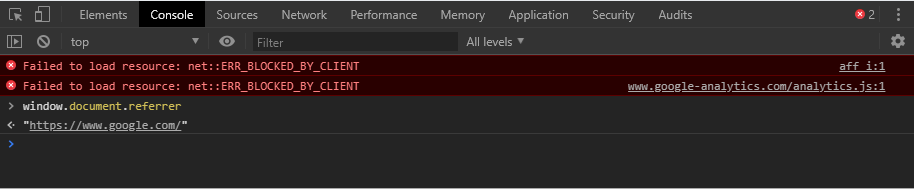
There are two ways a site can report to you the referrer they see: server-side or client-side.
If server-side, the referrer is looked up from the request headers, hence it will be spoofed.
If client-side (requires javascript code to be executed), the referrer will be looked up from document.referrer, hence not spoofed in Chromium due to browser bug.
Guessing they're picking the client-side value right ?
Yes, load https://www.myip.com/js/graf.js and scrolled to the end.
With Script-safe in place of uMatrix -
Seems the header is not sent at all or removed. I set the setting Block-click-through referrer to "On All Domains" for that to happen. Maybe you want to try this approach for a workaround.
I consider this a browser bug, this is what needs to be fixed. No reliable workaround can be crafted to match current referrer-spoofing feature -- at best, a workaround would be unreliable, i.e. easily bypassed by having script code executed at the top of a document, before uMatrix's own content script can patch the referrer according to current ruleset. I rather there be a real, actual fix than the appearance of one. My official suggestion would be to just use Firefox if rock-solid referrer spoofing is important.
No I'm fine, thought I would suggest one until document.referrer gets patched. So do you want me to keep it open ?
I consider this a browser bug, this is what needs to be fixed.
Can't find any bugs filed on the tracker. Do you know of any ?
Keep it open, I remembered there is this new Referrer-Policy header which appeared relatively recently, I need to investigate whether it can be used to implement uMatrix's referrer-spoofing.
With Script-safe in place of uMatrix
I looked into this, and I found that ScriptSafe adds a rel="no-referrer" to every link element in the DOM. Not sure what would happen if new link elements are dynamically added -- I didn't look further. Also unsure what would happen for when a location is navigated programmatically.
Is there any extension of Referrer Policy ? I want to see it in action once and see it deals.
Made a uBO-Scriptlet to patch document.referrer, useful on cases where document.referrer is used.
(function () {
let myRefer = '{{1}}';
window.document.__defineGetter__('referrer', function () {
return myRefer;
});
})();The extension Referer Control at https://chrome.google.com/webstore/detail/referer-control/hnkcfpcejkafcihlgbojoidoihckciin?hl=en is blocking the referer with success on 3rd party requests.
Yes, like this --
chrome.runtime.sendMessage({
type:"blockReferrer"
}, function (r) {
try {
if(r.block){
var meta = document.createElement('meta');
meta.name = "referrer";
meta.content = "no-referrer";
document.getElementsByTagName('head')[0].appendChild(meta);
}
} catch(ignore){}
});
@uBlock-user could you made this part from your uBO-Scriptlet?
It's better if the fix lands in the extension itself, rather than having to use a scriptlet in ublock.
I agreed.
I tried to play with the options in this Referer Control extension... I tested of few pages with which I had referer leakage with uMatrix before and seems to work well.
I am not sure if that can be implemented in uMatrix.
referrer-spoof not work in Chrome 72+, working on Chrome 71 now
@HashLiver Probably related to https://github.com/uBlockOrigin/uMatrix-issues/issues/74, fixed in dev build.
The extension Privacy Manager is working really well about hiding the referer in Chrome.
The uMatrix is not working of some pages. The referer control extension is working on every site tested but I had cases in which I had to disable the blocking the referrer string of third-party requests in order the page to work properly.
I don't know how they do but surprisingly, the Privacy Manager is working on every page tested.
Chrome 74 the referer is simple send to everyone https://www.whatismyreferer.com/.
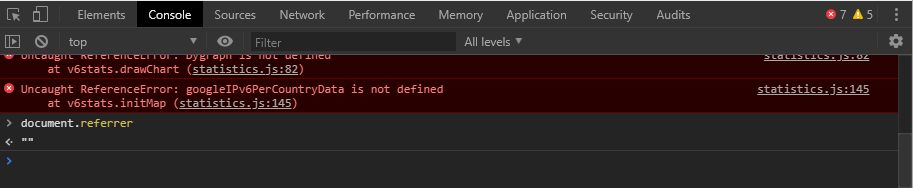
Apparently I can reproduce this on Firefox Nightly too --


@uBlock-user did you ever get this working on chrome? I have been trying a number of techniques to get around this to no avail.
Prerequisites
Description
Referrer leaks at
https://www.myip.com/when visited via google search result.A specific URL where the issue occurs
https://www.myip.com/Steps to Reproduce
https://www.google.com/https://www.myip.com/and scroll down to the end of the page to locate Referrer field showingURL: www.google.comSupporting evidence
Logger shows that REFERRER was blocked yet the website is able to detect.
Your environment