This issue is stale because it has been open 60 days with no activity. Remove stale label or comment or this will be closed in 5 days
Closed liangyi9812 closed 9 months ago
This issue is stale because it has been open 60 days with no activity. Remove stale label or comment or this will be closed in 5 days
Hi,您好,想明白了吗?
Verify Steps
OpenClash Version
v0.45.141-beta
Bug on Environment
Official OpenWrt
Bug on Platform
Linux-amd64(x86-64)
To Reproduce
Describe the Bug
未配置相关选项 (实验性:屏蔽 Google DNS 的局域网设备 IP 与 实验性:屏蔽 Google DNS 的局域网设备 Mac) 却出现了相关的nat防火墙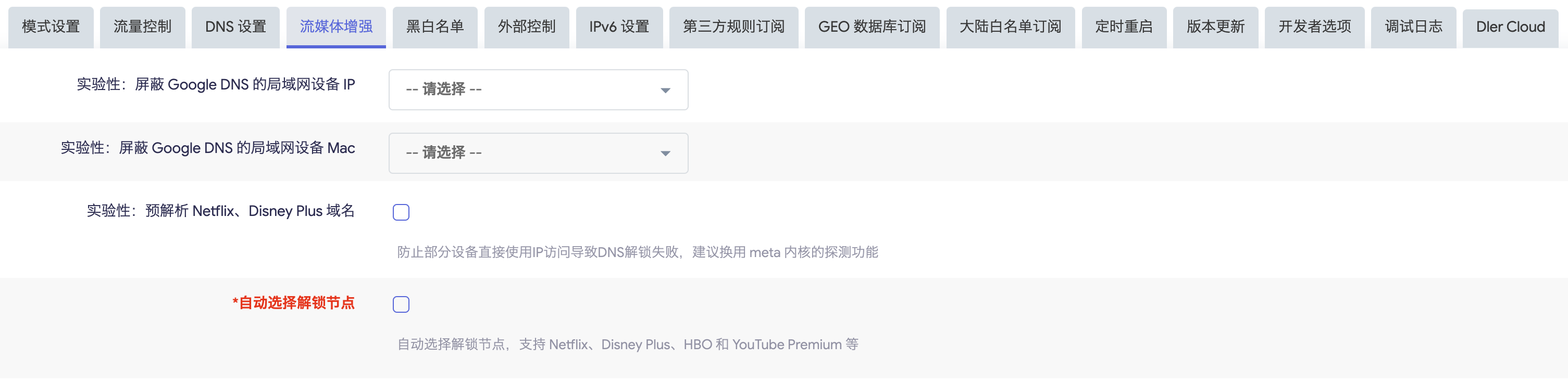

OpenClash Log
OpenClash 调试日志
生成时间: 2023-10-06 19:01:50 插件版本: v0.45.141-beta 隐私提示: 上传此日志前请注意检查、屏蔽公网IP、节点、密码等相关敏感信息
OpenClash Config
No response
Expected Behavior
未配置相关选项时不填加相关的NAT规则,以防混淆
Screenshots
No response