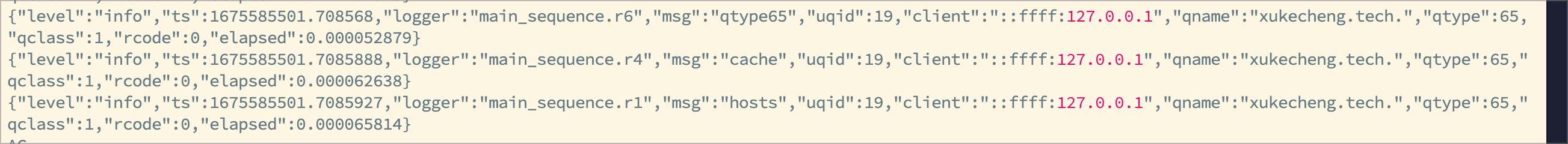
感谢分享,但我发现v5配置似乎有一处错误
- tag: "primary_forward"
type: sequence
args:
- exec: $forward_local
- exec: ttl 60-3600
- matches:
- "!resp_ip $geoip-cn"
- "!has_resp"
exec: drop_resp按照这个写法似乎不会丢弃 DNS 污染的返回结果,!has_resp 应该不需要取反,matches 条件多个时属于 AND 关系,即返回污染结果时应该是 (true AND false) 最终结果为 false ,不会丢弃结果
这个判断条件且取反真绕,想了好一会。

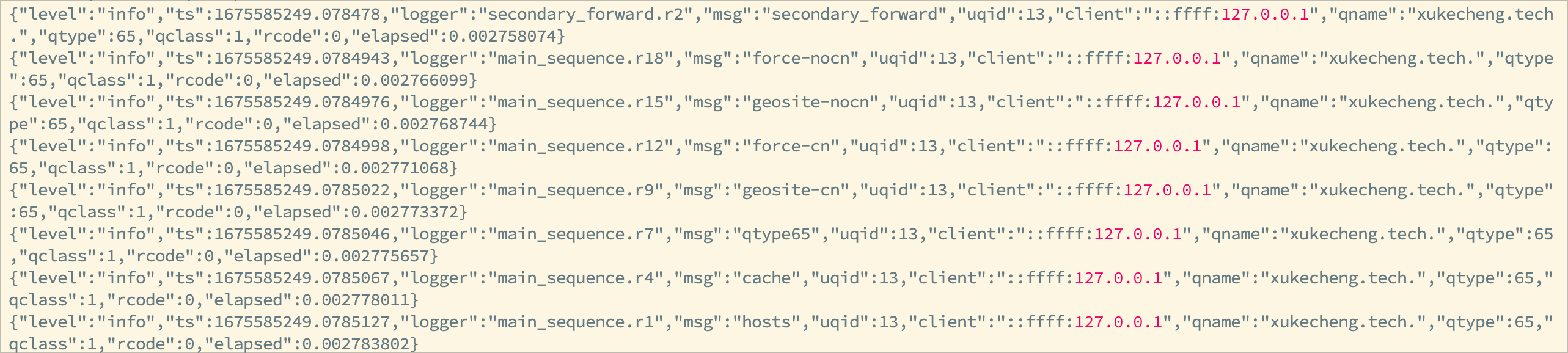
https://www.xukecheng.tech/use-mosdns-and-adguardhome-to-build-your-own-dns
国内的 DNS 服务商一般有两个,网络运营商和部分商业公司。而由于种种原因,这些 DNS 都存在或多或少的问题,这里就不细说了。而部分玩家为了尽可能地规避其中的某些问题,因此必不可少地需要自建 DNS 服务。