[TOC]
OpenID Connect Single Sign-On (SSO) NextCloud APP by Gluu
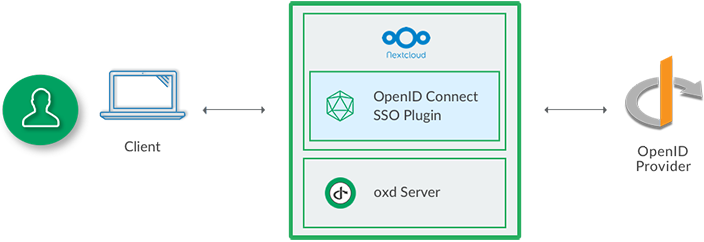
Gluu's OpenID Connect Single Sign-On (SSO) NextCloud APP will enable you to authenticate users against any standard OpenID Connect Provider (OP). If you don't already have an OP you can use Google or deploy the free open source Gluu Server.
Requirements
In order to use the NextCloud APP you will need a standard OP (like Google or a Gluu Server) and the oxd server.
-
Compatibility : 11.x version
Installation
Download
Unzip
If you have already package, unzip it to your NextCloud site root/apps folder.
Activate
Activate the app by performing the following steps:
- Go to
https://{site-base-url}/index.php/settings/apps - In tab
Not enabledfind OpenID Connect SSO APP By Gluu and click theEnablebutton.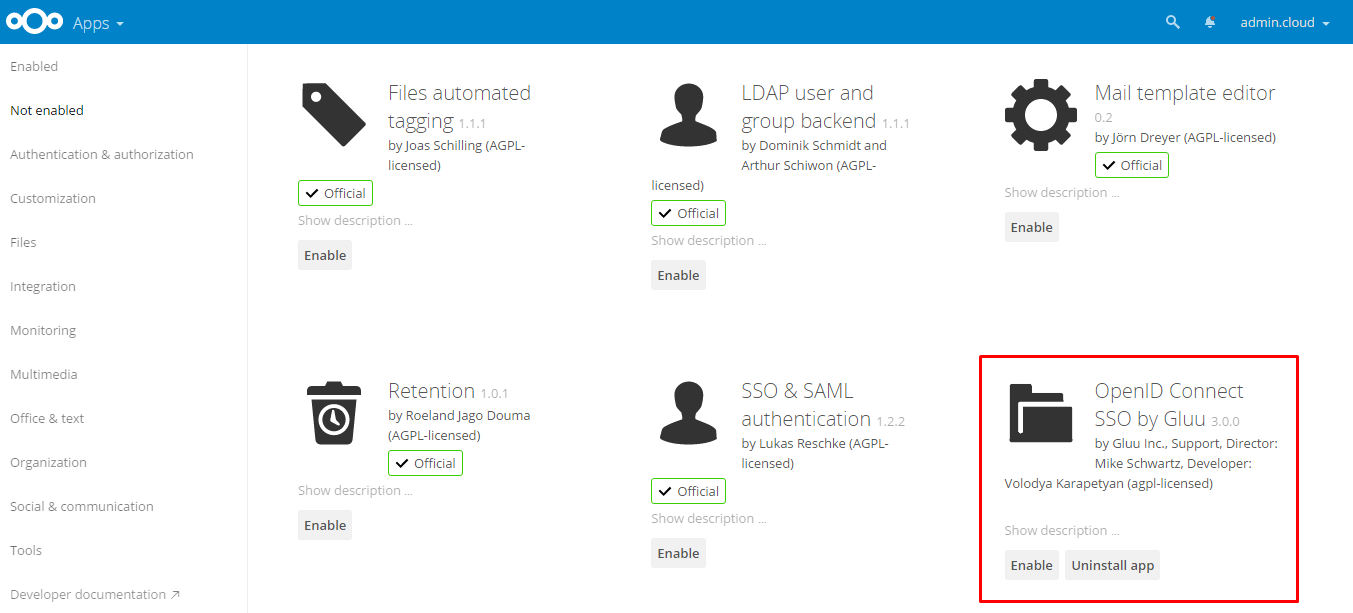
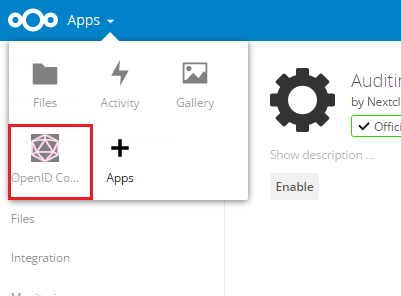
- Open menu tab OpenID Connect SSO
Configuration
General
In your NextCloud admin menu panel you should now see the OpenID Connect menu tab. Click the link to navigate to the General configuration page:
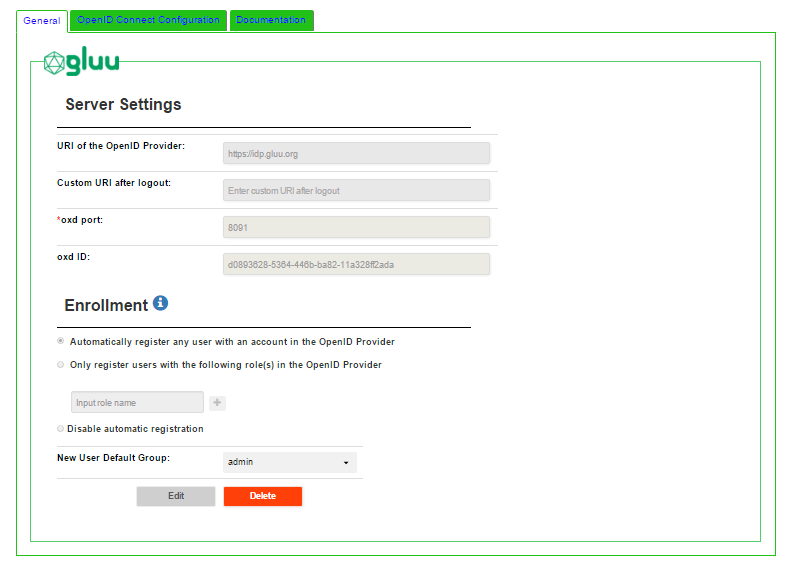
- Automatically register any user with an account in the OpenID Provider: By setting registration to automatic, any user with an account in the OP will be able to register for an account in your NextCloud site. They will be assigned the new user default role specified below.
- Only register and allow ongoing access to users with one or more of the following roles in the OP: Using this option you can limit registration to users who have a specified role in the OP, for instance
nextcloud. This is not configurable in all OP's. It is configurable if you are using a Gluu Server. Follow the instructions below to limit access based on an OP role. - New User Default Group: specify which Group to give to new users upon registration.
- URI of the OpenID Provider: insert the URI of the OpenID Connect Provider.
- Custom URI after logout: custom URI after logout (for example "Thank you" page).
- oxd port: enter the oxd-server port (you can find this in the
oxd-server/conf/oxd-conf.jsonfile). - Click
Registerto continue.
If your OpenID Provider supports dynamic registration, no additional steps are required in the general tab and you can navigate to the OpenID Connect Configuration tab.
If your OpenID Connect Provider doesn't support dynamic registration, you will need to insert your OpenID Provider client_id and client_secret on the following page.
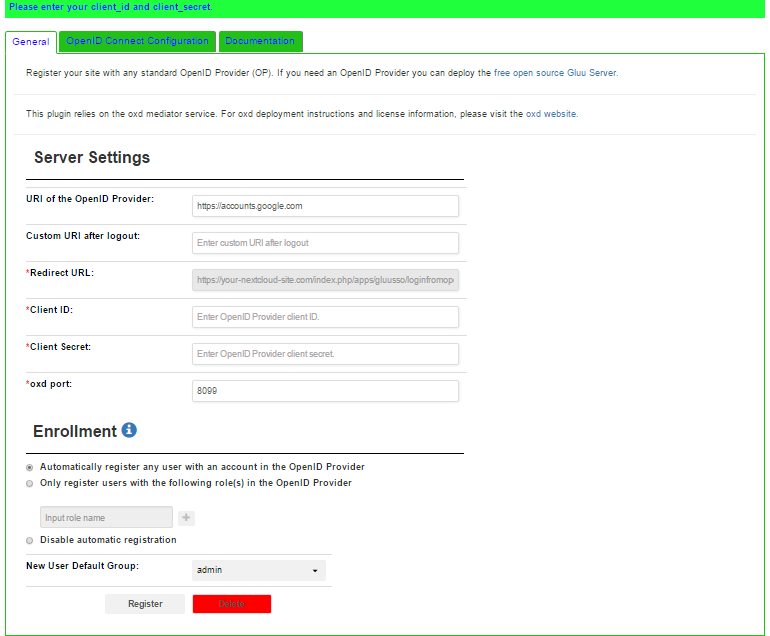
To generate your client_id and client_secret use the redirect uri: https://{site-base-url}/index.php/apps/gluusso/loginfromopenid.
If you are using a Gluu server as your OpenID Provider, you can make sure everything is configured properly by logging into to your Gluu Server, navigate to the OpenID Connect > Clients page. Search for your
oxd id.
Enrollment and Access Management
- Navigate to your Gluu Server admin GUI.
- Click the
Userstab in the left hand navigation menu. - Select
Manage People. - Find the person(s) who should have access.
- Click their user entry.
- Add the
User Permissionattribute to the person and specify the same value as in the app. For instance, if in the app you have limit enrollment to user(s) with role =nextcloud, then you should also haveUser Permission=nextcloudin the user entry. See a screenshot example. - Update the user record.
- Go back to the NextCloud APP and make sure the
permissionscope is requested (see below). - Now they are ready for enrollment at your NextCloud site.
OpenID Connect Configuration
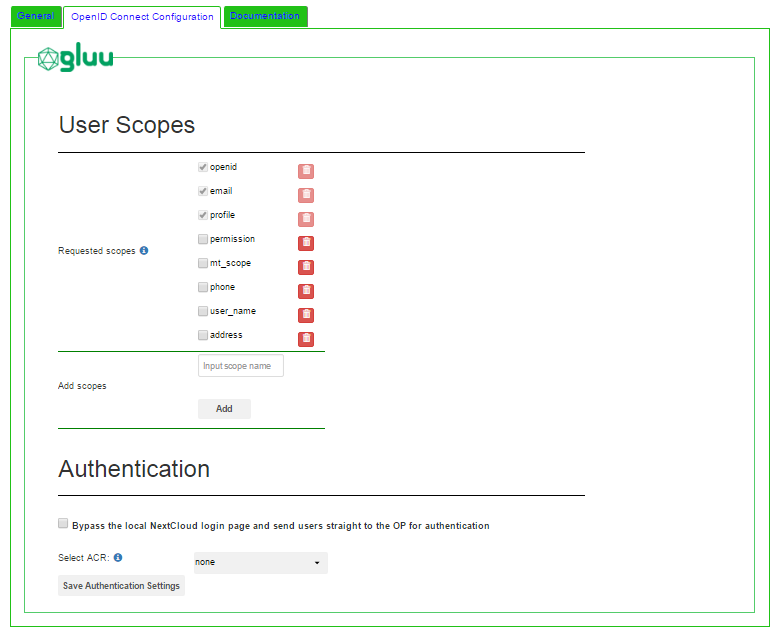
User Scopes
Scopes are groups of user attributes that are sent from the OP to the application during login and enrollment. By default, the requested scopes are profile, email, and openid.
To view your OP's available scopes, open a web browser and navigate to https://OpenID-Provider/.well-known/openid-configuration. For example, here are the scopes you can request if you're using Google as your OP.
If you are using a Gluu server as your OpenID Provider, you can view all available scopes by navigating to the OpenID Connect > Scopes interface inside the Gluu Server.
In the APP interface you can enable, disable and delete scopes.
Authentication
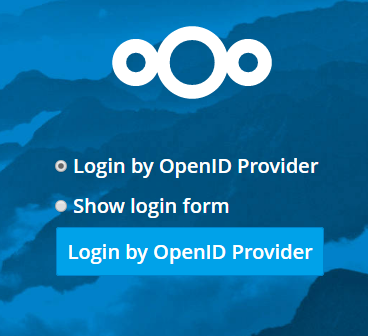
Bypass the local NextCloud login page and send users straight to the OP for authentication: Check this box so that when users attempt to login they are sent straight to the OP, bypassing the local NextCloud login screen. When it is not checked, users will see the following screen when trying to login:
Select ACR: To signal which type of authentication should be used, an OpenID Connect client may request a specific authentication context class reference value (a.k.a. "acr"). The authentication options available will depend on which types of mechanisms the OP has been configured to support. The Gluu Server supports the following authentication mechanisms out-of-the-box: username/password (basic), Duo Security, Super Gluu, and U2F tokens, like Yubikey.
Navigate to your OpenID Provider configuration webpage https://OpenID-Provider/.well-known/openid-configuration to see supported acr_values.
In the Select acr section of the app page, choose the mechanism which you want for authentication. If the Select acr value in the app is none, users will be sent to pass the OP's default authentication mechanism.