John the Ripper Packages
Openwall's John the Ripper (JtR) is a fast password cracker, currently available for many flavors of Unix and for Windows. Its primary purpose is to detect weak Unix passwords. Besides several crypt(3) password hash types most commonly found on various Unix systems, supported out of the box are Windows LM hashes, various macOS password hashes, as well as many non-hashes such as SSH private keys, encrypted filesystems such as macOS .dmg files and "sparse bundles", encrypted archives such as ZIP, RAR, and 7z, encrypted document files such as PDF and Microsoft Office's, plus lots of other hashes and ciphers.
Table of Contents

- Introduction
- Windows Package
- Snap Package
- macOS Package
- Flatpak Package
- Docker Image
- Checksums
- Package Security
- About This Project
- Contribute
- Acknowledgments and Contact
- License
Introduction
Continuous Delivery Status
We produce software in short cycles, ensuring that the software can be reliably released at any time, following a pipeline through a "production-like environment".
![Release Version][linkLatestReleaseVersion] | **Prerelease**
![Prerelease Version][linkLatestPrereleaseVersion] | | :-------------------------------------------: | :---------------------------------------------------------: | :-------------------------------------------------------------------: | | ![GitHub Total Downloads][linkTotalDownloads] | ![Release Date][linkLatestReleaseDate] | ![Prerelease Date][linkLatestPrereleaseDate] | ### Testing Packages | Available Technology | Rollout Status | | ------------------------------------ | ---------------------------------------------------- | | Docker image with the tag `bleeding` | [![Endpoint Badge][bleedingDocker]][linkRegistry] | | Snap package from the `edge` channel | [![Endpoint Badge][bleedingSnap]][linkSnapcraftJohn] |
Package Building Environments
Click on the link to learn more about our packages Building Environments.
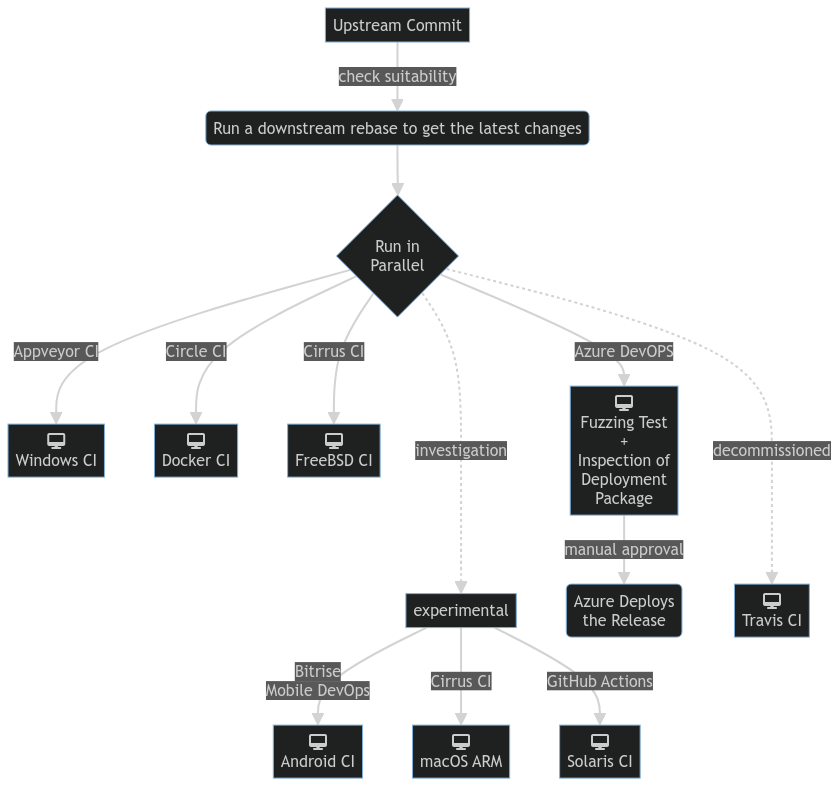
Testing and Continuous Integration
All continuous integration (CI) and continuous delivery (CD) procedures are fully automated, builds and tests are performed whenever requested by the packager. Manual procedures are required just to start the process.
Click on the link to learn more about our Continuous Integration and Continuous Delivery procedures.
Packaging and Application Distribution
Snap and Flatpak are cool new ways of distributing Linux applications among a wide range of different distros. They are technologies to deploy applications in a secure, sandboxed and containerized way.
A Docker image is a read-only template used to execute code in a Docker container. An image is an immutable file that contains the binaries, configuration files, libraries, dependencies, tools, and other files needed for John the Ripper application to run.
When the Docker user runs an image, it becomes one instance (it becomes a container, in other words, a running instance of the application).
📂 Windows
Delivered using Microsoft-hosted Windows 2022 Server in Azure \ Supported architecture: amd64
To install John the Ripper by downloading the .7z file and installing it manually, follow these steps:
- Download the compressed file to your machine.
- Navigate to where you downloaded the file and double-click the compressed file.
- Extract it to a directory such as
C:\john-the-ripper. - Start a command prompt.
- Navigate to the directory you extracted the compressed file, e.g.,
cd C:\john-the-ripper\run. - Run JtR:
C:\john-the-ripper\run>john --list=build-info
[...]
Build: cygwin 64-bit x86_64 AVX2 AC OMP OPENCL
SIMD: AVX2, interleaving: MD4:3 MD5:3 SHA1:1 SHA256:1 SHA512:1
[...] C:\john-the-ripper\run>john --test --format=SHA512crypt| 📑 More examples of running John The Ripper on Windows.
The highlights (👀):
- has fallback for CPU[*] and OMP;
- has OpenCL available (GPU driver installation is needed);
- generic crypt(3) format available;
- security feature Address Space Layout Randomisation (ASLR) enabled;
- security feature Data Execution Prevention (DEP) enabled.
[*] John the Ripper runs using the best SIMD instructions available on the host it's running on.
Windows Deployments
Using the instructions above, you can install the released version of john,
or the bleeding development version, or an earlier stable version on your system.
The package contains all the executables and libraries needed to run a fresh John the Ripper installation.
OpenSSF SLSA
SLSA is a framework intended to codify and promote secure software supply-chain practices, it helps trace software artifacts back to the build and source control systems that produced them. > :warning: **NOTE:** the release assets from our GitHub Releases are level 1 compliant.Running a non-OpenMP build on Windows
In some situations a non-OpenMP build may be faster. You can ask to fallback to a non-OpenMP build specifying the value of OMP_NUM_THREADS in the command-line. You avail the best SIMD instructions at one's disposal without any OpenMP stuff. E.g.:
PS C:\john-the-ripper\run> set OMP_NUM_THREADS=1
PS C:\john-the-ripper\run> .\john --list=build-infoAccessing OpenCL on Windows
If John the Ripper is not recognizing your GPU card:
- make sure all required GPU drivers are installed;
- restart your PC, if you have just installed the drivers.
📂 Snap
Delivered using Launchpad \ Supported architectures: amd64, arm64v8, ppc64le, riscv64, and s390x
A Snap is a gpg signed squashfs file containing an application together with its dependencies, and a description of how it should safely be run on your system.
You can install john by following the instructions at https://snapcraft.io/john-the-ripper.
For distributions without snap pre-installed, users should
enable snap support, then install:
sudo snap install john-the-ripperJust dance now:
$ john-the-ripper -list=build-info
[...]
Build: linux-gnu 64-bit x86_64 AVX2 AC OMP OPENCL
SIMD: AVX2, interleaving: MD4:3 MD5:3 SHA1:1 SHA256:1 SHA512:1
Deploy: sandboxed as a Snap app
[...]You can also run the software using the official john alias:
john -list=build-infoJohn runs confined under a restrictive security sandbox by default. Nevertheless, you can access and audit any file located in your home. Below, an usage example:
john -list=format-tests | cut -f3 > ~/allTests.in
john --format=SHA512crypt ~/allTests.inFor your convenience, the snap installed on your system contains the file
/snap/john-the-ripper/current/snap/manifest.yaml which field build_url
points to its build log.
The highlights (👀):
- has fallback for CPU[*] and OMP;
- has OpenCL available (GPU driver installation is needed);
- John the Ripper is a "featured software" in the security category on Canonical Snap Store;
- John the Ripper is a software with 4-star (⭐⭐⭐⭐) user reviews on Canonical Snap Store;
- John the Ripper is tagged as safe, confined and auditable software on Canonical Snap Store;
- John the Ripper supports and has a package for all architectures supported by Ubuntu itself.
- also available via the alias john, e.g.
john -list=build-info; - the latest released version:
- install from the Snapcraft
stablechannel.
- install from the Snapcraft
- a development version is also available:
- install from the Snapcraft
edgechannel.
- install from the Snapcraft
[*] John the Ripper runs using the best SIMD instructions available on the host it's running on.
John the Ripper snap package has approximately eight thousand active users [*].[*] 7 Day Active Users: the number of unique users who had at least one session within a 7 day period.
Enabling Aliases
You are free to pick and set up aliases. To enable the usage of aliases with John
the Ripper snap, run sudo snap alias john-the-ripper <alias>. For example:
sudo snap alias john-the-ripper john-snap
sudo snap alias john-the-ripper.dmg2john dmg2johnOnce enabled, John itself plus the *2john tools can be invoked using the aliases.
In the example, to run John type john-snap.
| 📑 More examples of enabling alias for John The Ripper snap.
Running a non-OpenMP build
In some situations a non-OpenMP build may be faster. You can ask to fallback to a
non-OpenMP build specifying OMP_NUM_THREADS=1 john <options> in the command-line.
You avail the best SIMD instructions at one's disposal without any OpenMP stuff. E.g.:
OMP_NUM_THREADS=1 john --list=build-infoAccessing OpenCL on Snap
As noted at https://forum.snapcraft.io/t/snaps-and-opencl/8509/17, the use of OpenCL by snaps is a problem. Support for NVIDIA cards is under development.
As a "general" solution (or in the case of AMD hardware), the user can run john
out of the sandbox, unconfined (e.g., run /snap/john-the-ripper/current/bin/john).
Snap Deployments
If you followed the instructions above, you have installed the released version of john
on your system. If you want to access the hot and bleeding development version of JtR,
you must follow the edge channel. For a clean install:
sudo snap install --channel=edge john-the-ripperIf you already have JtR installed:
sudo snap refresh --channel=edge john-the-ripperIf you do so, you will be running the development version available on GitHub.
📂 macOS
Delivered using Cirrus CI \ Supported architecture: arm64
To install John the Ripper by downloading the .7z file and installing it manually, follow these steps:
- Download the compressed file to your machine.
- Extract it to a directory such as
/Users/Me/bleeding. - Start a command prompt.
- Navigate to the directory you extracted the compressed file, e.g.,
cd /Users/Me/bleeding. - Run the software:
Install required Homebrew packages (if not already installed):
brew update
brew install libomp openssl gmpExecute John the Ripper:
$ run/john -list=build-info
[...]
Build: darwin22.6.0 64-bit arm ASIMD AC OMP OPENCL
SIMD: ASIMD, interleaving: MD4:2 MD5:2 SHA1:1 SHA256:1 SHA512:1
OMP fallback binary: john-arm64
[...]The highlights (👀):
- has fallback for CPU[*] (if that makes sense) and OMP;
- has OpenCL available;
- built using clang from the official Xcode toolchain plus non-system libraries from Homebrew.
[*] John the Ripper runs using the best SIMD instructions available on the host it's running on.
macOS Deployments
Using the instructions above, you can install the released version of john,
or the bleeding development version, or an earlier stable version on your system.
The package contains the necessary executables to run a fresh install of John the Ripper. You must install required Homebrew libraries.
OpenSSF SLSA
SLSA is a framework intended to codify and promote secure software supply-chain practices, it helps trace software artifacts back to the build and source control systems that produced them. > :warning: **NOTE:** the release assets from our GitHub Releases are level 1 compliant.Running a non-OpenMP build on macOS
In some situations a non-OpenMP build may be faster. You can ask to fallback to a non-OpenMP build specifying the value of OMP_NUM_THREADS in the command-line. You avail the best SIMD instructions at one's disposal without any OpenMP stuff. E.g.:
OMP_NUM_THREADS=1 run/john --list=build-info📂 Flatpak
Delivered using GitLab CI \ Supported architectures: amd64 and arm64v8
Flatpak is a new framework for desktop applications on Linux, built to be distribution agnostic and allow deployment on any Linux operating system out there.
Flatpak is available for the most common Linux distributions.
To install JtR download the john.flatpak file and run:
# Note that root privileges are required for some operations.
sudo dnf install -y flatpak # or 'yum install', 'apt-get install', etc.
sudo flatpak remote-add --if-not-exists flathub https://flathub.org/repo/flathub.flatpakrepo # flatpak repository
sudo flatpak install -y flathub org.freedesktop.Platform//24.08 # install the runtime (base "container")
flatpak --user install --bundle john.flatpak # per-user installation (not system wide)John runs confined under a restrictive security sandbox by default. Nevertheless, you can access and audit any file located in your home. Below, an usage example:
flatpak run com.openwall.John -list=build-info
flatpak run com.openwall.John -list=format-tests | cut -f3 > ~/allTests.in
flatpak run com.openwall.John --format=SHA512crypt ~/allTests.inThe highlights (👀):
- has fallback for CPU[*] and OMP;
- also available via FlatHub at https://flathub.org/apps/com.openwall.John.
[*] John the Ripper runs using the best SIMD instructions available on the host it's running on.
Flatpak Deployments
Using the instructions above, you can install the released version of john,
or the bleeding development version, or an earlier stable version on your system.
OpenSSF SLSA
SLSA is a framework intended to codify and promote secure software supply-chain practices, it helps trace software artifacts back to the build and source control systems that produced them. > :warning: **NOTE:** the release assets from our GitHub Releases are level 1 compliant.📂 Docker Image
Delivered using GitHub Actions \ Supported architectures: amd64 and arm64v8
Docker provides the ability to package and run an application in a loosely isolated environment called a container.
To use it:
# CPU and GPU formats
docker run -it ghcr.io/openwall/john:latest <binary id> <john options>
# To run ztex formats
docker run --device=/dev/ttyUSB0 ghcr.io/openwall/john:v1.9.0J1 ztex <john options>Run John the Ripper and check if it is working:
docker run ghcr.io/openwall/john # => uses the best SIMD available, tag 'latest' can be omitted
docker run ghcr.io/openwall/john:bleeding # => uses the latest bleeding release
docker run ghcr.io/openwall/john:latest best # => uses the best SIMD available| 📑 More examples of running John The Ripper on Docker.
The highlights (👀):
- OpenSSF SLSA 3 compliant;
- has NVIDIA OpenCL available (GPU driver is required on the host);
- has auto-selection of the best SIMD if user specifies
bestas the<binary id>:- example:
docker run ghcr.io/openwall/john:latest best -list=build-info.
- example:
- the latest released version:
- install from the command-line:
docker pull ghcr.io/openwall/john:latest.
- install from the command-line:
- a development version is also available:
- install from the command-line:
docker pull ghcr.io/openwall/john:bleeding.
- install from the command-line:
Docker Image Deployments
Using the instructions above, you can install the released version of john,
or the bleeding development version, or an earlier stable version on your system.
OpenSSF SLSA
SLSA is a framework intended to codify and promote secure software supply-chain practices, it helps trace software artifacts back to the build and source control systems that produced them. > :warning: **NOTE:** the Docker images from our GitHub Packages are level 3 compliant.Packages Checksums
Released packages checksums computed by Build Servers
File verification is the process of using an algorithm for verifying the integrity of a computer file. A popular approach is to store checksums (hashes) of files, also known as message digests, for later comparison. All john packages checksums (hashes) are computed by the CI servers.
By accessing the build logs for each release on GitHub releases you can view the hashes of all relevant files.
You can also go to https://github.com/openwall/john-packages/attestations for a list of our named artifacts along with their digest.
⚠ Security
Please inspect all packages prior to running any of them to ensure safety. We already know they're safe, but you should verify the security and contents of any binary from the internet you are not familiar with.
We take security very seriously.
About This Project
This project aims to create tools and procedures to automate the creation and enable traceability of packages for John the Ripper software, developing a CI and CD pipeline.
Contribute
We love contributions in the form of issues and pull requests. Read the Contributor Guide before contributing.
If you intend to report or contribute a fix related to security vulnerabilities, please first consult our Security Policy.
Upstream john project has a big backlog! If you're new to the project, maybe you'd
like to open a pull request to address one of them.
Acknowledgments and Contact
John the Ripper is proudly Powered by Open Source Community:
- Openwall and others.
License
GNU General Public License v2.0.