XNU Image Fuzzer
Last Updated: SUN 02 JUN 2024, 0800 EDT
Project Summary
The XNU Image Fuzzer Source Code contains a proof of concept implementation of an image fuzzer designed for XNU environments. It aims to demonstrate basic fuzzing techniques on image data to uncover potential vulnerabilities in image processing routines. The Objective-C Code implements 12 CGCreateBitmap & CGColorSpace Functions working with Raw Data and String Injection that are User Controllable Inputs.
- PermaLink https://srd.cx/xnu-image-fuzzer/
Build & Install Status
| Build OS & Device Info | Build | Install |
|---|---|---|
| macOS 14.5 X86_64 | ✅ | ✅ |
| macOS 14.5 arm | ✅ | ✅ |
| iPadOS 17.5 | ✅ | ✅ |
| iPhoneOS 17.5 | ✅ | ✅ |
| VisionPro 1.2 | ✅ | ✅ |
XNU Image Tools
- https://github.com/xsscx/xnuimagetools
- Create random images for fuzzing
Command Line Version
See URL https://github.com/xsscx/macos-research/tree/main/code/iOSOnMac
Project Support
- Open an Issue
Project Documentation
URL https://xss.cx/public/docs/xnuimagefuzzer/
whoami
- I am David Hoyt
Quick Start
- Open as Xcode Project or Clone
- Update the Team ID
- Click Run
- Share a File
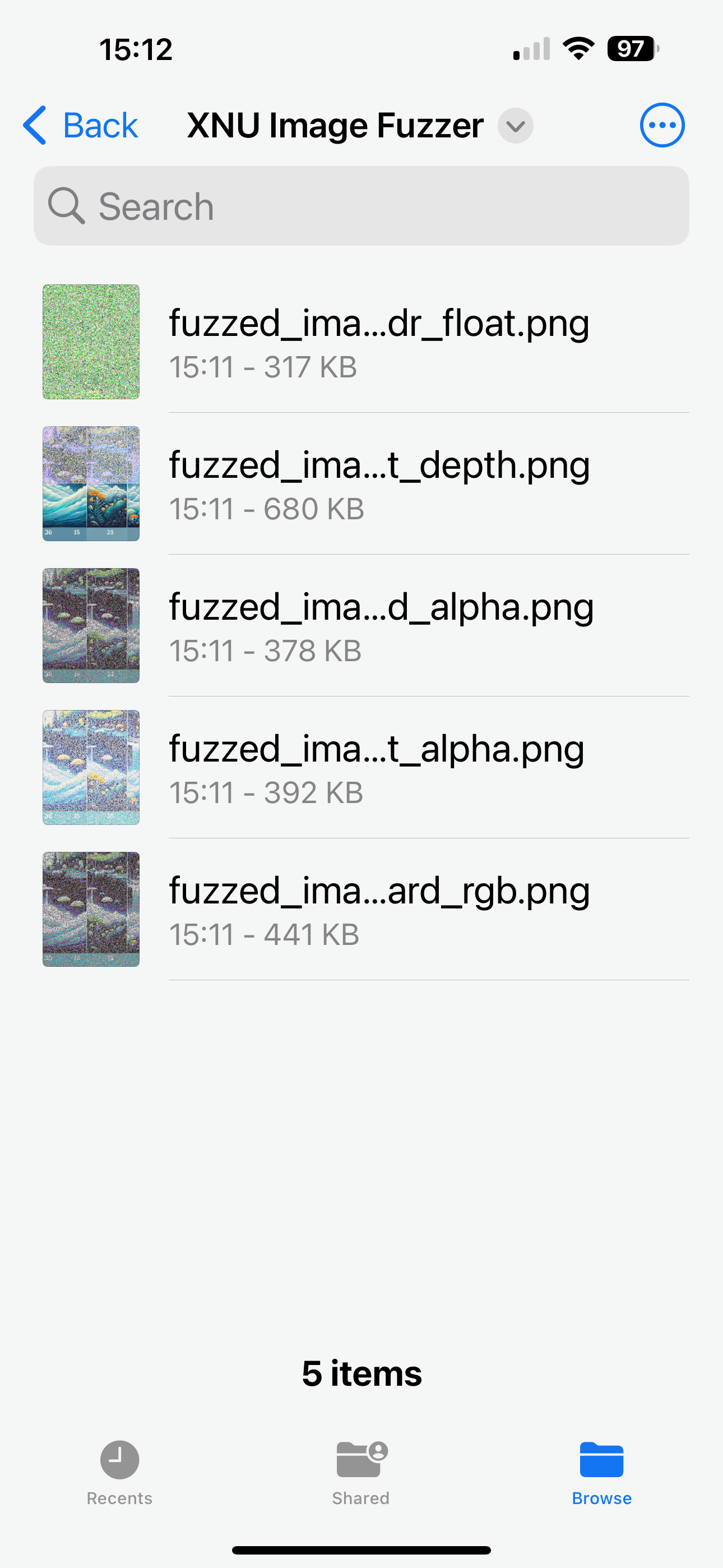
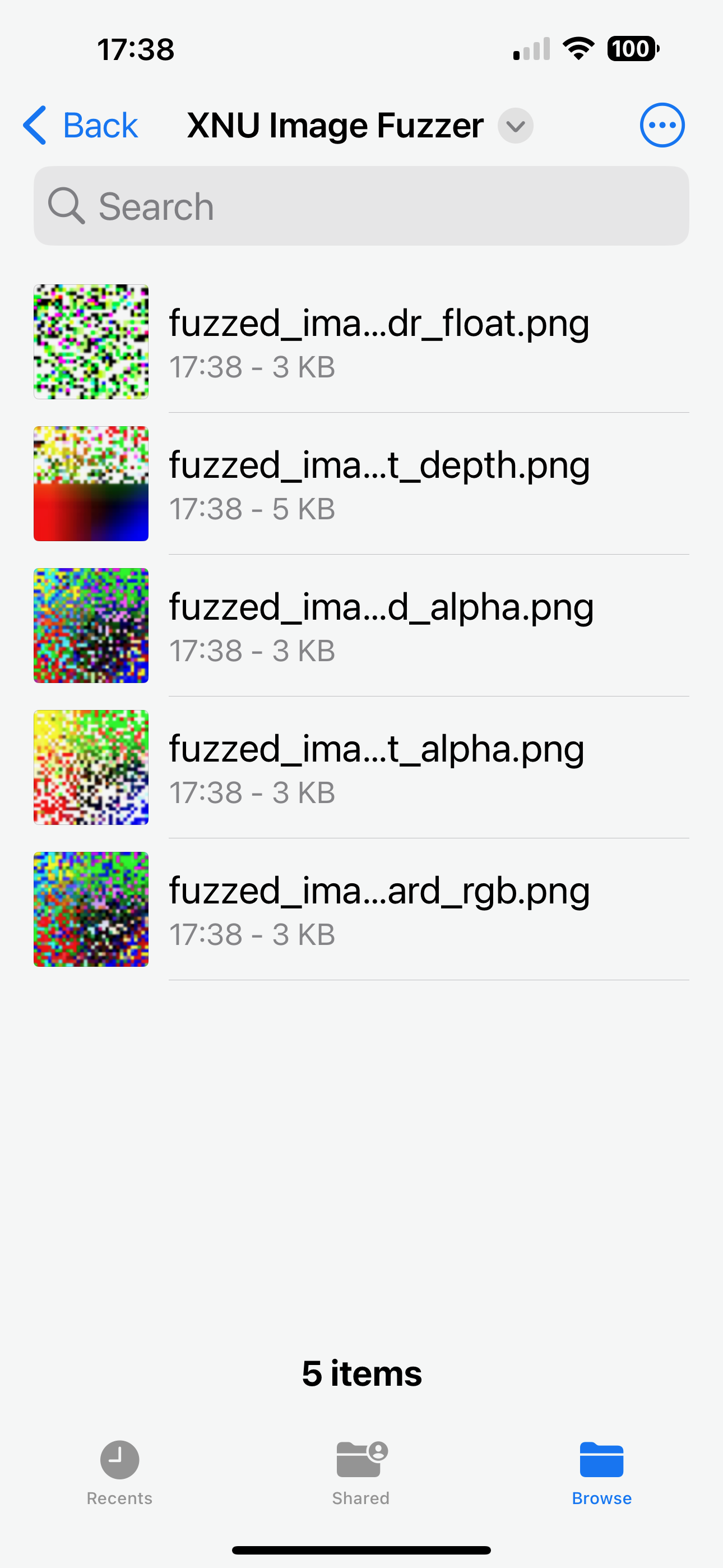
Copy Fuzzed Files
- Open the Files App on the Device
- Tap Share to Transfer the new Fuzzed Images to your Desktop
- Select All Files to AirDrop to your Desktop
- Screen Grab on iPhone 14 Pro MAX
How-to Rebuild Xcode Project
- Open Terminal
- Delete the Build Directories from the Project Folder
xnuimagefuzzer % rm -rf CMakeCache.txt CMakeFiles CMakeScripts cmake_install.cmake buildCreate a Test Folder
xnuimagefuzzer % mkdir xcode_buildCreate the Xcode Project
xnuimagefuzzer % cd xcode_build
xnuimagefuzzer/xcode_build % cmake -G Xcode ../XNU\ Image\ Fuzzer/CMakeLists.txt
-- The C compiler identification is AppleClang 15.0.0.15000309
-- The OBJC compiler identification is AppleClang 15.0.0.15000309
-- Detecting C compiler ABI info
-- Detecting C compiler ABI info - done
-- Check for working C compiler: /Applications/Xcode.app/Contents/Developer/Toolchains/XcodeDefault.xctoolchain/usr/bin/clang - skipped
-- Detecting C compile features
-- Detecting C compile features - done
-- Detecting OBJC compiler ABI info
-- Detecting OBJC compiler ABI info - done
-- Check for working OBJC compiler: /Applications/Xcode.app/Contents/Developer/Toolchains/XcodeDefault.xctoolchain/usr/bin/clang - skipped
-- Configuring done (8.8s)
-- Generating done (0.0s)
-- Build files have been written to: /Users/xss/Developer/xnuimagefuzzer/xcode_buildOpen the Project, Run
xcode_build % open xnuimagefuzzer.xcodeproj/Purpose of Using Fuzzed Images in Fuzzing
Overview
Embedding fault mechanisms into a generic image and further processing it through fuzzing enhances the effectiveness of testing by uncovering edge cases and potential vulnerabilities in image processing software.
Benefits
Uncovering Edge Cases
- Insight: Fuzzed images introduce a wide range of potential edge cases.
- Analysis: Helps uncover rare bugs and vulnerabilities that might only occur with specific, unanticipated inputs.
Testing Robustness and Stability
- Insight: Stress-tests the robustness of image processing algorithms.
- Analysis: Ensures the software can handle diverse and unexpected inputs without crashing or producing incorrect results.
Finding Security Vulnerabilities
- Insight: Targets specific vulnerabilities through fault injections.
- Analysis: Exposes security weaknesses, such as buffer overflows, by providing inputs that cause unexpected behavior.
Ensuring Compatibility with Various Formats
- Insight: Tests the software's ability to handle different image formats and types.
- Analysis: Reduces the risk of compatibility issues by providing comprehensive testing coverage.
Automating the Testing Process
- Insight: Integrates with automated fuzzing frameworks like Jackalope.
- Analysis: Enables continuous and scalable testing, improving software robustness over time.
Process
- Prepare the Image:
- Start with a generic image.
- Apply initial fuzzing to introduce random mutations.
- Embed specific fault mechanisms to target vulnerabilities.
- Submit to Fuzzing Harness:
- Load the processed image into a fuzzing framework like Jackalope.
- Configure the tool to use the image as a seed for further automated fuzzing.
- Monitor and Analyze:
- Monitor for crashes, hangs, and other signs of vulnerabilities.
- Collect and analyze the results to identify and understand the bugs found.
Conclusion
Using fuzzed images enhances fuzzing effectiveness by uncovering edge cases, testing robustness, finding security vulnerabilities, and ensuring compatibility with various formats. This approach provides comprehensive evaluation and helps create more resilient software.